55% Use Legitimate Credentials
Ransomware attacks now use valid credentials or exploit unknown vulnerabilities.
Call a Specialist Today! 888-785-4405 | Free Shipping!

Powerful, AI-driven security that detects, investigates, and stops multi-stage, multi-vector cyberattacks across your entire environment.
Protect your endpoints, users, email, cloud, identity, and network with an AI-native XDR platform built to outpace modern adversaries.
Gartner Customers' Choice 2025 • MITRE ATT&CK Strong Performer • IDC MarketScape Leader
Sophos XDR overview (3:42)
Attackers are moving faster, stealthier, and more strategically than ever
Ransomware attacks now use valid credentials or exploit unknown vulnerabilities.
Attackers remain undetected for a week on average (2025 Sophos IR team).
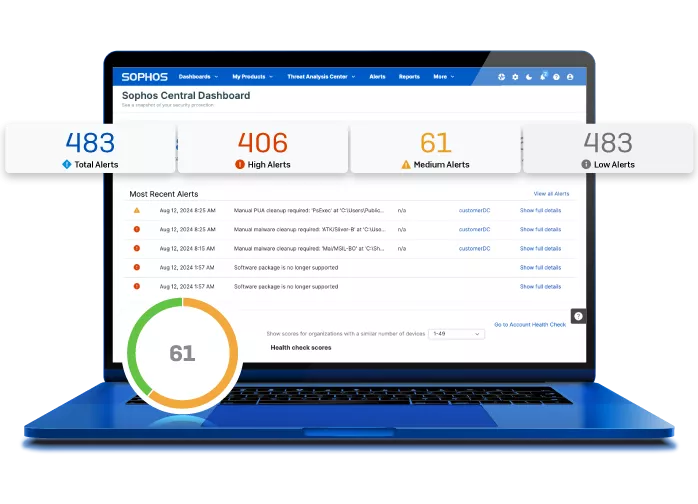
Organizations struggle with security team fatigue from alert overload.
Sophos XDR gives your team the speed, clarity, and intelligence needed to stop adversaries earlier in the attack chain.
A powerful, open XDR platform designed to detect sophisticated threats quickly and stop them even faster
Real-time insights contextualize alerts and recommend next steps.
High-risk activities rise to the top automatically across all attack surfaces.
Every detection mapped to ATT&CK tactics to expose gaps.
Correlates detections from endpoints, network, email, cloud, and identity.
Process termination, network isolation, and ransomware rollback.
Tightens defenses when hands-on-keyboard behavior is detected.
Disable accounts, reset passwords, contain email, block domains.
Investigate and respond to threats directly within M365 environments.

Sophos' AI-native architecture accelerates every stage of detection and response.
Sophos XDR ingests and correlates data across Sophos and non-Sophos technologies
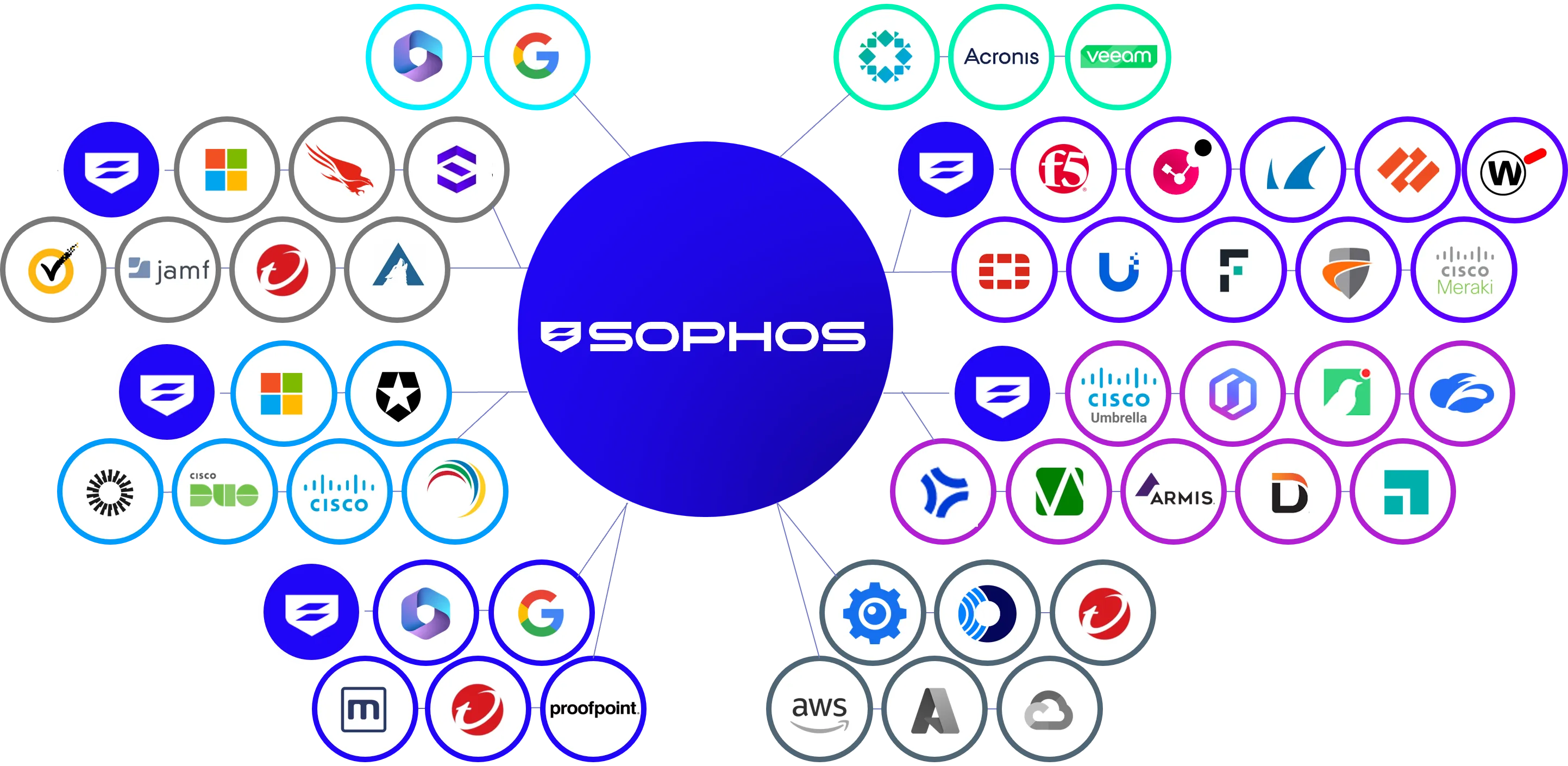
Endpoint, Firewall & NDR, ZTNA, Email Security, Cloud & Workload Protection, Mobile, Phishing & Training
Microsoft 365, Google Workspace, Identity providers, Network and firewall vendors, Cloud security, Backup and recovery, Productivity platforms
Watch how Sophos XDR correlates detections from a non-Sophos firewall, email filtering tool, and Sophos Endpoint into one unified case enabling faster, more confident remediation.
Attack simulation demo (5:56)
Sophos XDR focuses on prevention + detection + response, not just telemetry collection
| Feature / Capability | Sophos XDR | CrowdStrike Falcon Insight | SentinelOne Singularity | Microsoft Defender XDR |
|---|---|---|---|---|
| Integrated Endpoint Protection Included | ||||
| AI Assistant for Investigation | ||||
| Automated Case Correlation Across Vendors | ||||
| Adaptive Attack Protection | ||||
| Ransomware Rollback | ||||
| Deep Microsoft 365 Response Actions | ||||
| Built-In Zero-Touch Prevention | ||||
| Flexible Licensing for SMB & Enterprise |
Choose Sophos XDR if you want:

Extend detection and response with integrated services and controls
24/7 threat hunting and response from world-class analysts working on your behalf.
Learn moreIdentity threat detection & response with dark-web credential exposure checks and misconfiguration detection.
Learn moreBest-in-class endpoint prevention included automatically with XDR.
Learn moreOur specialists will help you choose the right XDR configuration, licenses, and optional MDR services
Comprehensive guides to help strengthen your XDR strategy
Quick overview of features, AI capabilities, and integration options.
Download PDFWatch how Sophos XDR correlates multi-vector attacks in real time.
Watch nowLatest ransomware trends and how XDR helps organizations respond faster.
View reportStop multi-stage attacks, eliminate blind spots, and empower your team with AI-driven detection and response.
Talk to a specialist