
XG Firewall
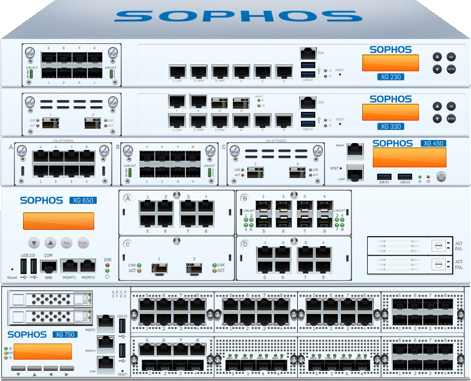
XG Series hardware appliances provide industry leading performance at every price point with the ultimate in flexibility, connectivity and reliability.

Synchronized Security In A Connected World
Synchronized Security: Cybersecurity as a System
Pouring more and more money into individual point security solutions is no longer a realistic long-term solution. While standalone cybersecurity solutions can address specific vectors of attack, cybercriminals will continue to be able to exploit the gaps between point solutions and take advantage of the lack of connectivity. Organizations need a layered approach to security, one where products connect and share information. It’s time to embrace this new approach. It’s time for Synchronized Security.
Synchronized Security is cybersecurity as a system. Security solutions connect with each other in real time via a Security Heartbeat™, working together to combat advanced threats. This automation enhances your defenses, responding automatically to events, so you can mitigate risk and slash the time and effort spent managing IT security. Only through connecting the big cybersecurity dots in this way can you create a system that transcends point challenges and enables you to create long-term security strategies that work for your business.
Synchronized Security is built on three pillars: Discover, Analyze, and Respond. These pillars enable security components to become more than the sum of their parts by working together to stay ahead of the attackers.
Synchronized Security in Action
The more security services that share real-time information in a Synchronized Security system, the more you can benefit from their inter-connectivity. Here are three of the ways Synchronized Security elevates your protection while simplifying IT security management.
- Slash incident response time: 3.3 hours to 8 seconds
- Take back control of your network
- Reduce risk from mobile devices
Click here to read the full version of "Synchronized Security In A Connected World".

Discover unknown threats
Security solutions automatically share information to reveal hidden risks and unknown threats.

Analyze data in real time
Real-time incident analysis and cross-estate reporting delivers instant insights

Respond automatically to incidents
Adaptive policies automatically respond to infections and incidents in seconds.







